
Endpoint detection and response is one of the best ways to protect your company's data. But with so many endpoint detection software available, which should you choose? We have created a list for you that includes top 5 endpoint detection & response softwares in 2021.
What is Endpoint Detection & Response Software?
Endpoint Detection & Response Software is a type of software that monitors the endpoint technology. It detects any malicious files, suspicious activities and much more to protect companies from data loss or network damage due to malware attacks. These Endpoint Detection & Response (EDR) softwares can deliver real-time protection against cyber threats, data breaches, system failures, and even theft.
1. SentinelOne Endpoint Protection Platform

SentinelOne is the only cybersecurity solution encompassing AI-powered prevention, detection, response and hunting across endpoints, containers, cloud workloads, and IoT devices in a single autonomous platform. With SentinelOne, organizations gain full transparency into everything happening across the network at machine speed – to defeat every attack, at every stage of the threat lifecycle. When attackers come after your privacy, intellectual property, infrastructure, and collaborative modes of working, they assault more than just data. You’re under attack, and so are your values. That’s why SentinelOne is dedicated to keeping their breakthrough platform ahead of threats from every vector. Gartner, NSS Labs, and industry leading organizations recognize that their approach sets them apart.
2. Sophos Intercept X: Next-Gen Endpoint

Sophos Intercept X is the world’s most comprehensive endpoint protection solution. Built to stop the widest range of attacks, Intercept X has been proven to prevent even the most advanced ransomware and malware by leveraging a unique combination of next-generation techniques. This includes the ability to detect never-before-seen malware with deep learning, stop ransomware with Sophos anti-ransomware technology, and deny attacker tools with signatureless exploit prevention. Intercept X also includes root cause analysis to provide insight into threats, and instant malware removal to ensure no attack remnants remain.
3. MVISION Endpoint Security
McAfee Endpoint Security delivers industry-leading protection and operational simplicity for your diverse endpoint environment.
4. VMware Carbon Black EDR
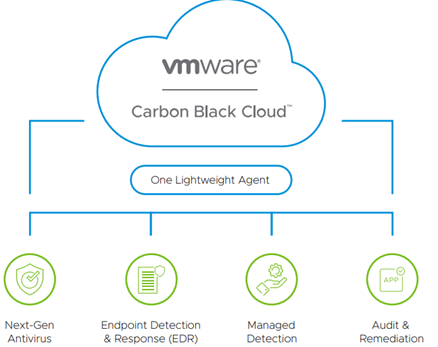
CB Response is the market-leading incident response and threat hunting solution designed to provide responders with the most information possible, accompanied by expert threat analysis and armed with real-time response capabilities to stop attacks, minimize damage and close security gaps. CB Response makes these teams more efficient, reducing investigations from days to hours, and more effective, enabling them to discover threats before attacks can exploit them. CB Response also allows teams to connect to and isolate infected machines to prevent lateral movement and remediate devices without costly IT involvement.
5. Microsoft Defender for Endpoint
Microsoft Defender for Endpoint is a complete endpoint security solution that delivers preventative protection, post-breach detection, automated investigation, and response. With Defender for Endpoint, you have: Agentless, cloud powered - No additional deployment or infrastructure. No delays or update compatibility issues. Always up to date. Unparalleled optics - Built on the industry’s deepest insight into Windows threats and shared signals across devices, identities, and information. Automated security - Take your security to a new level by going from alert to remediation in minutes—at scale.
Conclusion
Endpoint detection and response softwares are effective for protecting against cyber threats. Each endpoint detection software has their own specific features to best suit the needs of companies depending on what they want from one an endpoint detection & response software. Organizations need to assess their security policies, company priorities, data sensitivity levels, cost factors, technical capacities etc., before deciding which one to move forward with. We hope this blog helped you make that decision. For more information on these softwares, contact us for assistance.

